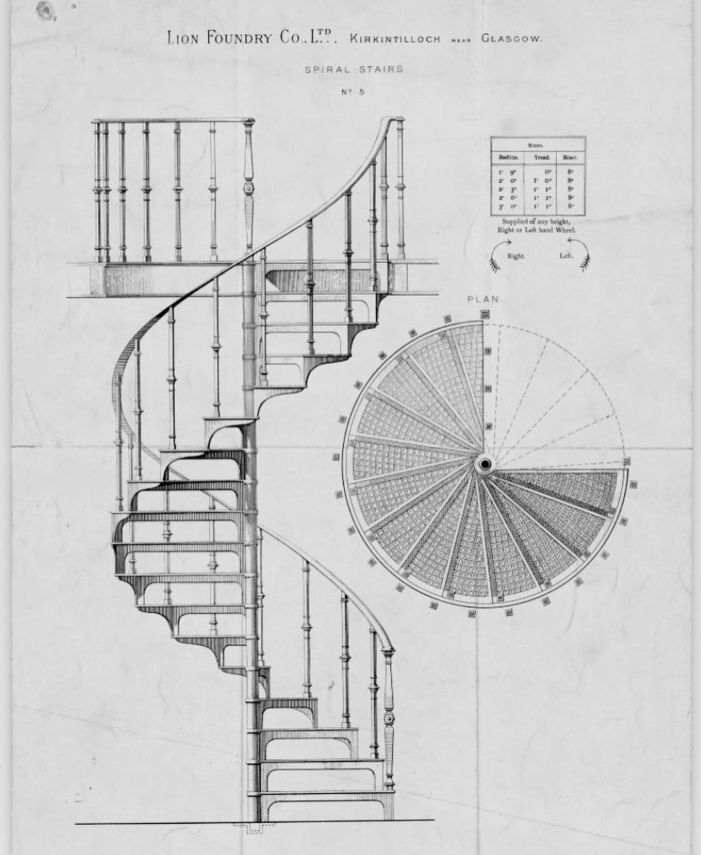
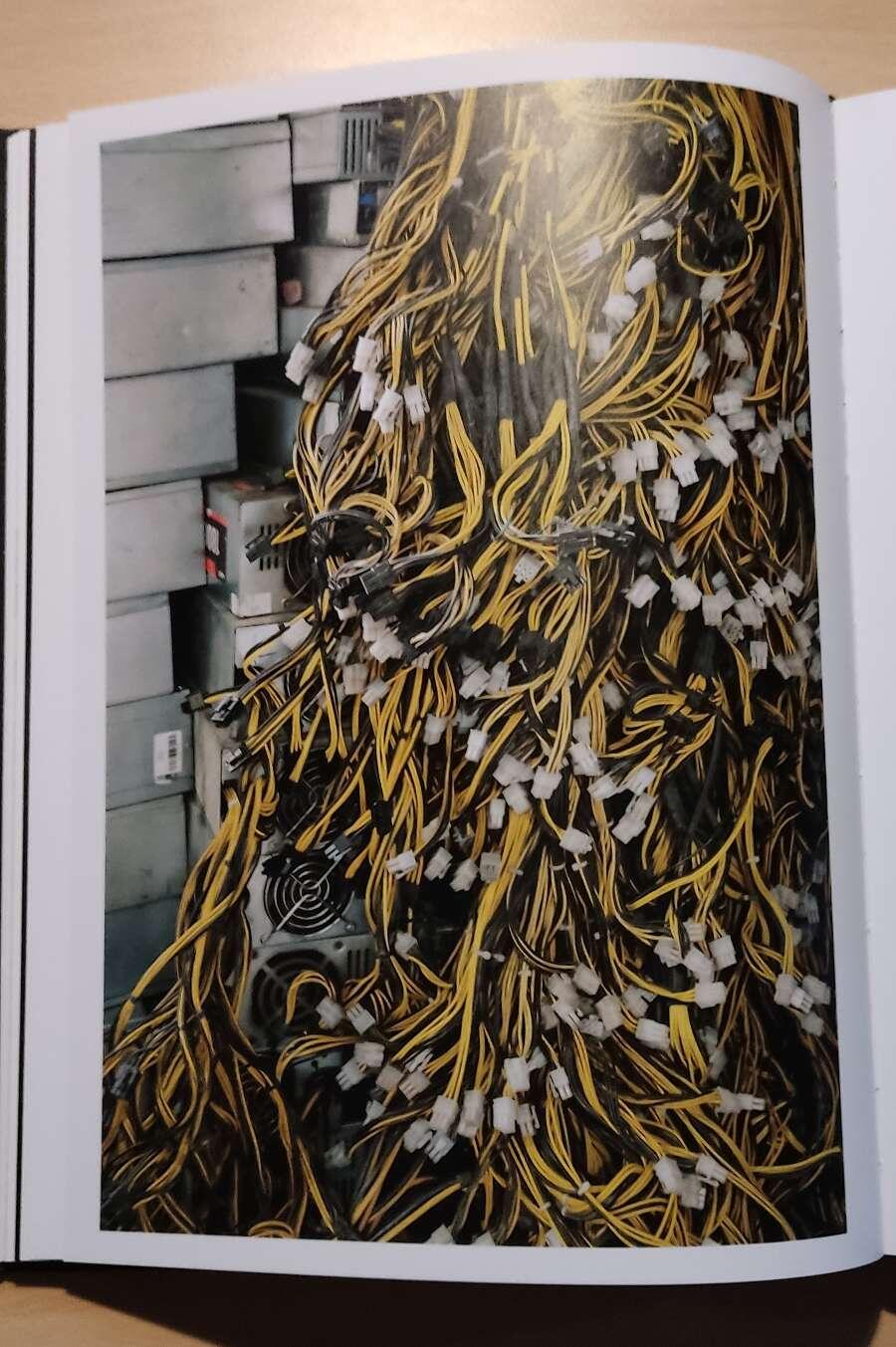
I saw this machine in real life, and it was gorgeous.

GM.

Cell Towers vs WiFi.
In this wicked useful and brand spanking new post, I'm going to teach you what data is being shared from cell towers vs WiFi, and what your options to reduce that are. The end has 3 example cellphone setups for the average person, somewhat savvy, and tinfoil hat.
~~~
When you connect to cellphone towers:
You're using the modem which has an IMEI identification number. Using a DeGoogled phone and a VPN does NOT change this from revealing info about the hardware TO the TOWER, such as where it was bought. And who bought it.
There's a couple ways to deal with this. One way is to buy it in cryptocurrency, from a company like mine. This is the easiest method for most people.
A second way is to use external hotspots for service, and buy those locally in cash. For example GLinet travel routers:
https://simplifiedprivacy.com/glinet/index.html
(or crypto like Calyx/Tmobile depending on your country.) Some prefer this because then they can put it in a faraday bag to hide their location at home. And only take it out of the faraday bag outside their house.
A third way is to change the IMEI. This method is controversial, as some say it's stealth. Others say you're drawing attention to yourself by giving them bullshit or previous numbers.
Some devices are easier to change then others. And some countries have made it illegal to change the IMEI. Of course, I can not recommend anything illegal. But if it is legal in your country, then generally older things such as Nokias are the easiest. LunarDAO has a guide on this:
https://wiki.lunardao.net/imei.html
A combination of the 2nd and 3rd way can be done by using something like Blue Merle. This is software for GLiNET travel routers that changes the IMEI of the router. Then you could in theory swap different SIM cards. However, this has a high risk of potential error for a new user, and it's unclear who's audited it:
https://github.com/srlabs/blue-merle
~~~
When you connect to WiFi:
You're NOT using the IMEI. Instead, you're getting a MAC address assigned to you by the router. This is a local area network. Android randomly generates MAC addresses for each connection, and you can actually see these in the settings of the WiFi connection.
In general, Android security is pretty good for WiFi. However, the CIA loves to hack routers. From the Wikileaks documents, we know they prefer to tunnel traffic from home routers directly to the CIA to see the traffic.
There's two main ways to avoid this. First, you could always use a VPN, which then bypasses the router's DNS.
Second, you could always be behind a firewall or travel router. The router's WAN port is the one communicating with a modem (public internet). While the router's LAN or (local area network) is the one giving you a MAC address.
~~~
What are some example setups?
average person:
Phone (bought with Crypto)
\/
SIM (bought with cash)
\/
VPN
\/
JMP Chat (VoIP)
(using public xmpp servers)
\/
Cell numbers
~~~~~
Savvy dude:
Phone (bought with Crypto)
\/
Silent Link (Crypto eSIM)
\/
VPN
\/
VPS you control
self-host xmpp
\/
JMP Chat (VoIP)
\/
Cell numbers
~~~~~
Tinfoil hat:
Phone (bought with Crypto)
No SIM. Using Tor
\/
GLiNET router w/ SIM (Using VPN)
maybe faraday bags or IMEI changes
\/
VPS you control
self-host xmpp
\/
JMP Chat (VoIP)
\/
Cell numbers
~~~~~
And of course, regular SMS is horrible. Go with a real messenger if the other person will allow it, (which one is actually not that critical): Signal, XMPP, Matrix, Session, SimpleX.
Self-hosting the VPS just provides another layer of protection that you control between the hostile adversary and you.
So our team can help you get a Phone, or setup a VPS:
https://simplifiedprivacy.com/they-see-everything/index.html
But even if you go with another option, I hope you digest my core message:
you've got way more control than you think.
Nice.
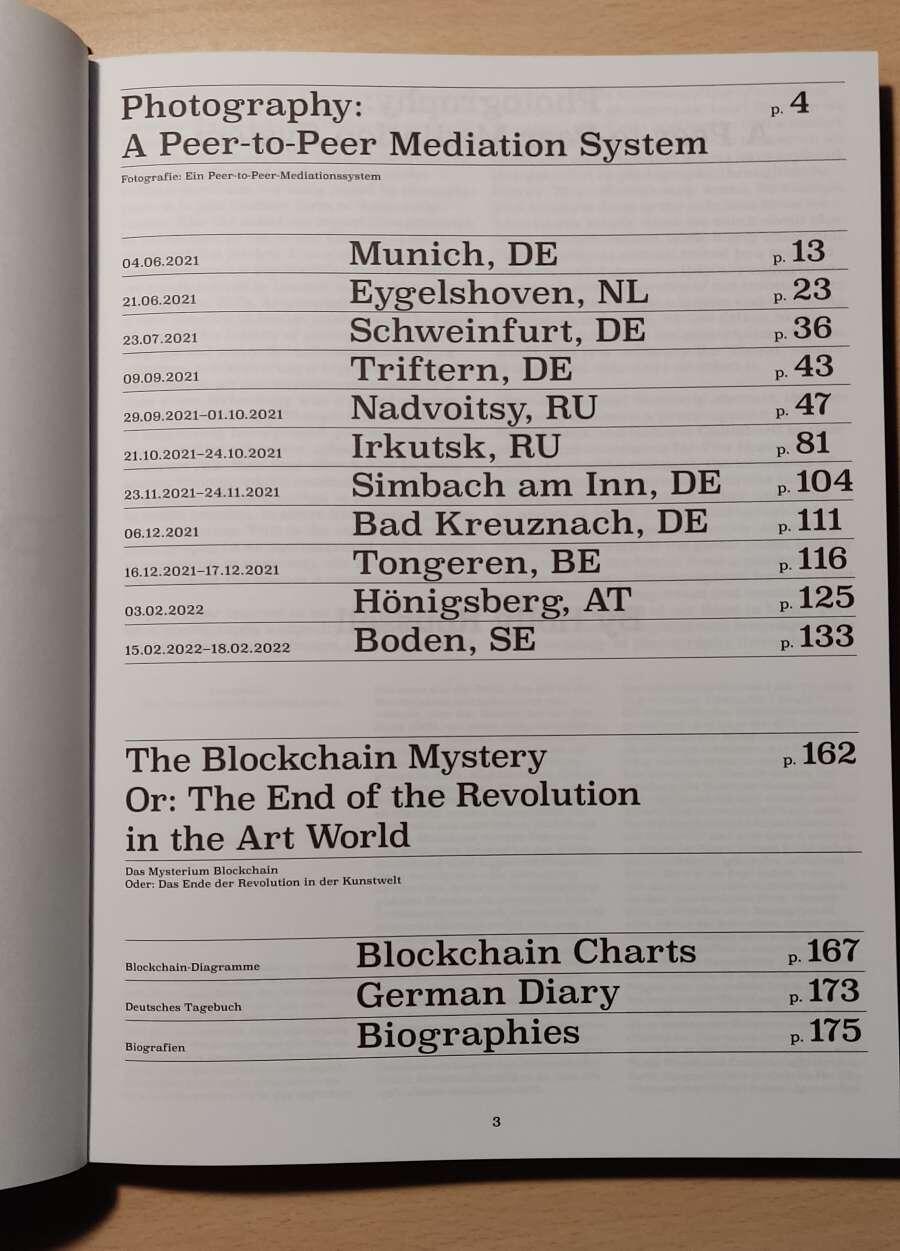
Hold each one in your hand.
Does it spark joy?
GM.

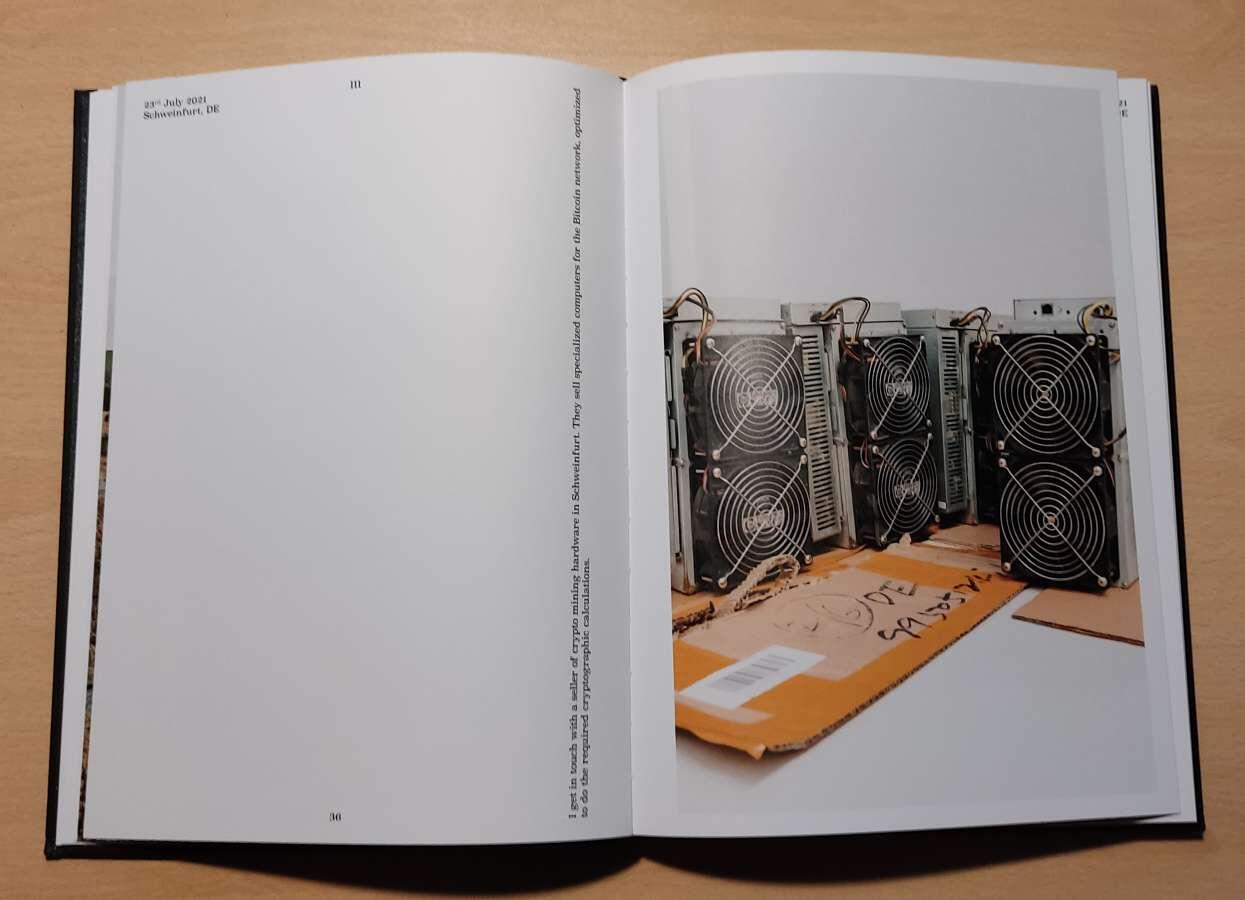
Some personal clients I haven't put out into the public yet. They are light duty, so it could be a setup that doesn't scale well, but for now it seems to be working fine.
I had a chat with nostr:nprofile1qqsg2zqd8wkhpnxu6lm5c2dyfa2mhpwte57apjae2ldp6g2mmwf3ypqpzamhxue69uhhyetvv9ujuurjd9kkzmpwdejhgtck0cpm9 about Bitcoin, Cashu, nostr, and privacy, and it was pretty good!
Thank you for having me 🫡
Loved this!
There needs to be a nuclear power that embraces an open internet with open finance.
Imagine a nuclear power that hosted an open #cashu mint, #fedimint, or crypto exchange that anyone in the world could access. Anyone in the world can connect to their servers. If a country like the United States requested that these servers be shut down, limit access, or that developers were extradited, the hosting country would just say "Bugger off".
Once a nuclear power hosts and defends a free internet, we are really off to the races, as it would require other countries to maintain a North Korea style firewall to contain its own citizens.
United States - 3,708 warheads
Russia - 5,977 warheads
China - 350 warheads
France - 290 warheads
United Kingdom - 190 warheads
Pakistan - 165 warheads
India - 156 warheads
Israel - 90 warheads (Israel has never publicly confirmed or denied its nuclear status)
North Korea - 60 warheads
An obvious answer here is Russia. They are already sanctioned by the west, and don't have much more to loose, and to gain, they could become the new financial center of the world.
I would think that the main hindrance here is that the nuclear country would not want it's own citizens accessing open finance.
Hmmm, I've been using indexeddb via Dexie.js.
All of my relay handling routines store events into Dexie and then my UI is generated off from Svelte/Dexie LiveQueries from DB changes.
This conceptually keeps relays separate from ui, and works well for PWAs. Probably not the fastest though.
This looks great